Table of Contents
During your IT interview, you may be asked to state the difference between symmetric and asymmetric key cryptography. This article goes through the basic similarities, differences, advantages, and disadvantages of symmetric and asymmetric encryption key systems.
*This post may contain affiliate links. As an Amazon Associate we earn from qualifying purchases.
The Difference Between Symmetric and Asymmetric Key Cryptography – Main Facts
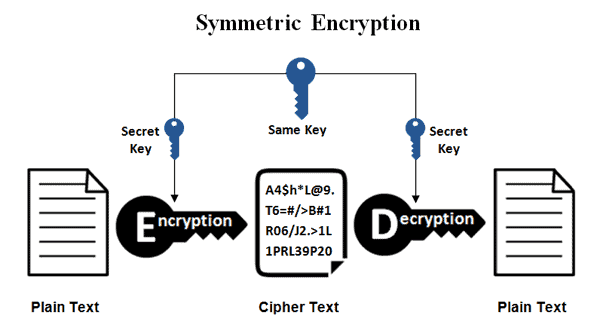
Symmetric key cryptography (also called Secret key cryptography) features one key that two people can use to encrypt and decrypt data send between themselves. All parties who want to decrypt the cyphertext need to have access to the secret key to use symmetric key cryptography for confidential communication.
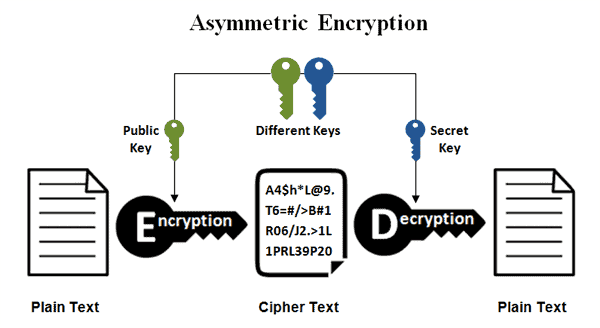
Asymmetric key cryptography (also called Public key cryptography) utilizes two keys. One of the keys is public and is used for encrypting data, while the second key is private and it is used for decrypting the data.
Advantages and Disadvantages of Symmetric Key Cryptography
Symmetric key cryptography is very accessible and easy to use. There is one key shared between two people. While this could be extremely convenient, the confidentiality it manages to achieve is actually limited. The core disadvantage of symmetric key cryptography is that confidentiality depends entirely on the two people or parties who share the code.
If one of them shares the code with a third party, confidentiality is breached. Moreover, the more the two people use the key to encrypt data on the Internet, the more vulnerable the information is. This happens because the same key can be used to decrypt data.
Advantages and Disadvantages of Asymmetric Key Cryptography
With asymmetric keys, data can be encrypted by using a public key and the decrypted by using a secret key. At the same time, the data can be encrypted by using the secret key and then decrypted by using the public key.
The secret key is unique for the user, so it is up to him and how he/she uses it to keep up confidentiality. Compared to symmetric key cryptography, public key cryptography is more useful to keep messages private. On the other hand, it is also much slower and requires considerably more processing. This is the fundamental difference between symmetric and asymmetric encryption.
Also read:
- How does Google’s face recognition work?
- What are the differences between web server and application server?
- What does ‘pushing the envelope’ mean??
Conclusion
This is a short, yet informative response to the?symmetric vs asymmetric encryption interview question. After reading this, you should be able to answer any interview questions regarding the fundamental differences between symmetric and asymmetric cryptography key systems as well as the main advantages and disadvantages of each one.